DOS memory management
This article needs additional citations for verification. (March 2011) |
In
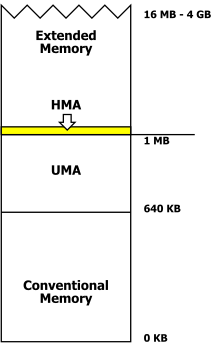
The 640 KiB limit imposed great complexity on hardware and software intended to circumvent it; the physical memory in a machine could be organised as a combination of base or conventional memory (including lower memory), upper memory, high memory (not the same as upper memory), extended memory, and expanded memory, all handled in different ways.
Conventional memory
The
On the IBM PC, all the address space up to 640 KiB was available for RAM. This part of the address space is called "conventional memory" since it is accessible to all versions of DOS automatically on startup. Segment 0, the first 64 KiB of conventional memory, is also called
Upper memory area
The upper memory area (UMA) refers to the address space between 640 and 1024 KiB (0xA0000–0xFFFFF). The 128 KiB region between 0xA0000 and 0xBFFFF was reserved for
For example, the monochrome video adapter memory area ran from 704 to 736 KiB (0xB0000–0xB7FFF). If only a monochrome display adapter was used, the address space between 0xA0000 and 0xAFFFF could be used for RAM, which would be contiguous with the conventional memory.[3]
The system BIOS ROMs must be at the upper end of the address space because the CPU starting address is fixed by the design of the processor. The starting address is loaded into the program counter of the CPU after a hardware reset and must have a defined value that endures after power is interrupted to the system. On reset or power up, the CPU loads the address from the system ROM and then jumps to a defined ROM location to begin executing the system power-on self-test, and eventually load an operating system.
Since an
Expanded memory
As memory prices declined, application programs such as
Allocation and use of expanded memory was not transparent to application programs. The application had to keep track of which bank of expanded memory contained a particular piece of data, and when access to that data was required, the application had to request (through a driver program) the expanded memory board to map that part of memory into the processor's address space. Although applications could use expanded memory with relative freedom, many other software components such as drivers and terminate-and-stay-resident programs (TSRs) were still normally constrained to reside within the 640K "conventional memory" area, which soon became a critically scarce resource.
The 80286 and the high memory area
When the
As a result, some DOS programs would no longer work. To maintain compatibility with the PC and XT behavior, the AT included an A20 line gate (Gate A20) that made memory addresses on the AT wrap around to low memory as they would have on an 8088 processor. This gate could be controlled, initially through the keyboard controller, to allow running programs which were designed for this to access an additional 65,520 bytes (64 KiB) of memory in real mode. At boot time, the BIOS first enables A20 when counting and testing all of the system's memory, and disables it before transferring control to the operating system. Enabling the A20 line is one of the first steps a protected mode x86 operating system does in the bootup process, often before control has been passed onto the kernel from the bootstrap (in the case of Linux, for example).
The high memory area (HMA) is the
Originally, the logic gate was a gate connected to the
Disconnecting A20 would not wrap all memory accesses above 1 MiB, just those in the 1 MiB, 3 MiB, 5 MiB, etc. ranges. Real mode software only cared about the area slightly above 1 MiB, so Gate A20 was enough.
The first user of the HMA among Microsoft products was Windows 2.0 in 1987, which introduced the HIMEM.SYS device driver. Starting with versions 5.0 of DR-DOS (1990) and of MS-DOS (1991), parts of the operating system could be loaded into HMA as well, freeing up to 46 KiB of conventional memory. Other components, such as device drivers and TSRs, could be loaded into the upper memory area (UMA).
A20 handler
The A20 handler is software controlling access to the high memory area.
A20 gate on later processors
The
80386 and subsequent processors
Intel processors from the
On 386 and subsequent processors, memory managers like QEMM might move the bulk of the code for a driver or TSR into extended memory and replace it with a small fingerhold that was capable of accessing the extended-memory-resident code. They might analyze memory usage to detect drivers that required more RAM during startup than they did subsequently, and recover and reuse the memory that was no longer needed after startup. They might even remap areas of memory normally used for memory-mapped I/O. Many of these tricks involved assumptions about the functioning of drivers and other components. In effect, memory managers might reverse-engineer and modify other vendors' code on the fly. As might be expected, such tricks did not always work. Therefore, memory managers also incorporated very elaborate systems of configurable options, and provisions for recovery should a selected option render the PC unbootable (a frequent occurrence).
Installing and configuring a memory manager might involve hours of experimentation with options, repeatedly rebooting the machine, and testing the results. But conventional memory was so valuable that PC owners felt that such time was well-spent if the result was to free up 30 or 40 KiB of conventional memory space.
Extended memory
In the context of IBM PC-compatible computers, extended memory refers to memory in the address space of the 80286 and subsequent processors, beyond the 1 megabyte limit imposed by the 20 address lines of the 8088 and 8086. Such memory is not directly available to DOS applications running in the so-called "real mode" of the 80286 and subsequent processors. This memory is only accessible in the protected or virtual modes of 80286 and higher processors.
See also
- Global EMM Import Specification(GEMMIS)
- Virtual DMA Services (VDS)
- Virtual Control Program Interface (VCPI)
- Extended Virtual Control Program Interface(XVCPI)
- DOS Protected Mode Interface (DPMI)
- DOS Protected Mode Services (DPMS)
- Helix Cloaking
References
- ISBN 1-56529-932-9.
- ^ "Memory Map (x86) - OSDev Wiki". wiki.osdev.org. Retrieved 2020-12-20.
- ^ ISBN 0-7897-1903-7.
- ISBN 0-201-55447-X.
External links
- Microsoft support: Overview of Memory-Management Functionality in MS-DOS
- Computer Chronicles (1990). "High Memory Management". From the Internet Archive.
