Data breach
A data breach, also known as data leakage, is "the unauthorized exposure, disclosure, or loss of
Attackers have a variety of motives, from financial gain to
The first reported breach was in 2002 and the number occurring each year has grown since then. A large number of data breaches are never detected. If a breach is made known to the company holding the data, post-breach efforts commonly include containing the breach, investigating its scope and cause, and notifications to people whose records were compromised, as required by law in many jurisdictions. Law enforcement agencies may investigate breaches, although the hackers responsible are rarely caught.
Many criminals sell data obtained in breaches on the
Definition
A data breach is a violation of "organizational, regulatory, legislative or contractual" law or policy
History and prevalence

Before the widespread adoption of data breach notification laws around 2005, the prevalence of data breaches is difficult to determine. Even afterwards, statistics per year cannot be relied on because data breaches may be reported years after they occurred,[8] or not reported at all.[9] Nevertheless, the statistics show a continued increase in the number and severity of data breaches that continues as of 2022[update].[10] In 2016, researcher Sasha Romanosky estimated that data breaches (excluding phishing) outnumbered other security breaches by a factor of four.[11]
The first reported data breach occurred in April 2002
In the 2000s, the
Perpetrators
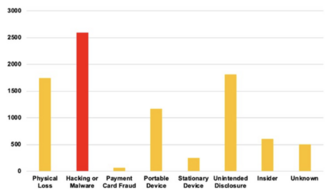
According to a 2020 estimate, 55 percent of data breaches were caused by
Causes
Technical causes
Despite developers' goal of delivering a product that works entirely as intended, virtually all
Vulnerabilities vary in their ability to be
Many data breaches occur on the hardware operated by a partner of the organization targeted—including the
Human causes
Human causes of breach are often based on trust of another actor that turns out to be malicious.
Another source of breaches is accidental disclosure of information, for example publishing information that should be kept private.[44][45] With the increase in remote work and bring your own device policies, large amounts of corporate data is stored on personal devices of employees. Via carelessness or disregard of company security policies, these devices can be lost or stolen.[46] Technical solutions can prevent many causes of human error, such as encrypting all sensitive data, preventing employees from using insecure passwords, installing antivirus software to prevent malware, and implementing a robust patching system to ensure that all devices are kept up to date.[47]
Breach lifecycle
Prevention
Although attention to security can reduce the risk of data breach, it cannot bring it to zero. Security is not the only priority of organizations, and an attempt to achieve perfect security would make the technology unusable.[48] Many companies hire a chief information security officer (CISO) to oversee the company's information security strategy.[49] To obtain information about potential threats, security professionals will network with each other and share information with other organizations facing similar threats.[50] Defense measures can include an updated incident response strategy, contracts with digital forensics firms that could investigate a breach,[51] cyber insurance,[52][7] and monitoring the dark web for stolen credentials of employees.[53] In 2024, the United States National Institute of Standards and Technology (NIST) issued a special publication, "Data Confidentiality: Identifying and Protecting Assets Against Data Breaches".[54] The NIST Cybersecurity Framework also contains information about data protection.[55] Other organizations have released different standards for data protection.[56]
The architecture of a company's systems plays a key role in deterring attackers. Daswani and Elbayadi recommend having only one means of
The principle of least persistence[64]—avoiding the collection of data that is not necessary and destruction of data that is no longer necessary—can mitigate the harm from breaches.[65][66][67] The challenge is that destroying data can be more complex with modern database systems.[68]
Response
A large number of data breaches are never detected.[69] Of those that are, most breaches are detected by third parties;[70][71] others are detected by employees or automated systems.[72] Responding to breaches is often the responsibility of a dedicated computer security incident response team, often including technical experts, public relations, and legal counsel.[73][74] Many companies do not have sufficient expertise in-house, and subcontract some of these roles;[75] often, these outside resources are provided by the cyber insurance policy.[76] After a data breach becomes known to the company, the next steps typically include confirming it occurred, notifying the response team, and attempting to contain the damage.[77]
To stop exfiltration of data, common strategies include shutting down affected servers, taking them offline,
Gathering data about the breach can facilitate later litigation or criminal prosecution,
Notifications are typically sent out as required by law.
Consequences
For consumers
After a data breach, criminals make money by selling data, such as usernames, passwords, social media or customer loyalty account information, debit and credit card numbers,[26] and personal health information (see medical data breach).[93] Criminals often sell this data on the dark web, using platforms like .onion or I2P.[94] This information may be used for a variety of purposes, such as spamming, obtaining products with a victim's loyalty or payment information, identity theft, prescription drug fraud, or insurance fraud.[95] The threat of data breach or revealing information obtained in a data breach can be used for extortion.[26]
Consumers may suffer various forms of tangible or intangible harm from the theft of their personal data, or not notice any harm.
For organizations

There is little empirical evidence of economic harm from breaches except the direct cost, although there is some evidence suggesting a temporary, short-term decline in stock price.[101] Other impacts on the company can range from lost business, reduced employee productivity due to systems being offline or personnel redirected to working on the breach,[102] resignation or firing of senior executives,[87] reputational damage,[87][103] and increasing the future cost of auditing or security.[87] Consumer losses from a breach are usually a negative externality for the business.[104] Some experts have argued that the evidence suggests there is not enough direct costs or reputational damage from data breaches to sufficiently incentivize their prevention.[105][106]
Estimating the cost of data breaches is difficult, both because not all breaches are reported and also because calculating the impact of breaches in financial terms is not straightforward. There are multiple ways of calculating the cost to businesses, especially when it comes to personnel time dedicated to dealing with the breach.[107] Author Kevvie Fowler estimates that more than half the direct cost incurred by companies is in the form of litigation expenses and services provided to affected individuals, with the remaining cost split between notification and detection, including forensics and investigation. He argues that these costs are reduced if the organization has invested in security prior to the breach or has previous experience with breaches. The more data records involved, the more expensive a breach typically will be.[108] In 2016, researcher Sasha Romanosky estimated that while the mean breach cost around the targeted firm $5 million, this figure was inflated by a few highly expensive breaches, and the typical data breach was much less costly, around $200,000. Romanosky estimated the total annual cost to corporations in the United States to be around $10 billion.[109]
Laws
Notification
The law regarding data breaches is often found in legislation to protect privacy more generally, and is dominated by provisions mandating notification when breaches occur.[110] Laws differ greatly in how breaches are defined,[3] what type of information is protected, the deadline for notification,[6] and who has standing to sue if the law is violated.[111] Notification laws increase transparency and provide an reputational incentive for companies to reduce breaches.[112] The cost of notifying the breach can be high if many people were affected and is incurred regardless of the company's responsibility, so it can function like a strict liability fine.[113]
As of 2024[update], Thomas on Data Breach listed 62
Security safeguards
Measures to protect data from a breach are typically absent from the law or vague.[110] Filling this gap is standards required by cyber insurance, which is held by most large companies and functions as de facto regulation.[115][116] Of the laws that do exist, there are two main approaches—one that prescribes specific standards to follow, and the reasonableness approach.[117] The former is rarely used due to a lack of flexibility and reluctance of legislators to arbitrate technical issues; with the latter approach, the law is vague but specific standards can emerge from case law.[118] Companies often prefer the standards approach for providing greater legal certainty, but they might check all the boxes without providing a secure product.[119] An additional flaw is that the laws are poorly enforced, with penalties often much less than the cost of a breach, and many companies do not follow them.[120]
Litigation
Many
See also
- Full disclosure (computer security)
- Medical data breach
- Surveillance capitalism
- Data breaches in India
References
- ^ a b Solove & Hartzog 2022, p. 5.
- ^ a b Fowler 2016, p. 2.
- ^ a b Solove & Hartzog 2022, p. 41.
- ^ Shukla et al. 2022, pp. 47–48.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, p. 18.
- ^ a b Solove & Hartzog 2022, p. 42.
- ^ a b Fowler 2016, p. 45.
- ^ Solove & Hartzog 2022, p. 18.
- ^ Solove & Hartzog 2022, p. 29.
- ^ Solove & Hartzog 2022, pp. 17–18.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, p. 9.
- ^ Joerling 2010, p. 468 fn 7.
- ^ Lesemann 2010, p. 206.
- ^ Lesemann 2010, pp. 206–207.
- ^ Joerling 2010, pp. 468–469.
- ^ Seaman 2020, pp. 6–7.
- ^ a b Solove & Hartzog 2022, p. 40.
- ^ Davidoff 2019, "Modern dark data brokers".
- ^ Solove & Hartzog 2022, p. 21.
- ^ Howell, Christian Jordan; Maimon, David (2 December 2022). "Darknet markets generate millions in revenue selling stolen personal data, supply chain study finds". The Conversation. Retrieved 22 April 2024.
- ^ Solove & Hartzog 2022, p. 23.
- ^ Solove & Hartzog 2022, p. 26.
- ^ Kaster & Ensign 2023, p. 355.
- ^ Crawley 2021, p. 46.
- ^ Fowler 2016, pp. 7–8.
- ^ a b c Fowler 2016, p. 13.
- ^ Fowler 2016, pp. 9–10.
- ^ Fowler 2016, pp. 10–11.
- ^ Ablon & Bogart 2017, p. 1.
- ^ a b Ablon & Bogart 2017, p. 2.
- ^ a b Daswani & Elbayadi 2021, p. 25.
- ^ Seaman 2020, pp. 47–48.
- ^ Daswani & Elbayadi 2021, pp. 26–27.
- ^ Sloan & Warner 2019, pp. 104–105.
- ^ Daswani & Elbayadi 2021, p. 19–22.
- ^ Daswani & Elbayadi 2021, p. 15.
- ^ Ntantogian, Malliaros & Xenakis 2019.
- ^ a b Daswani & Elbayadi 2021, pp. 22–23.
- ^ a b Fowler 2016, pp. 19–20.
- ^ a b Sloan & Warner 2019, p. 94.
- ^ Makridis 2021, p. 3.
- ^ Daswani & Elbayadi 2021, pp. 16–19.
- ^ Sloan & Warner 2019, pp. 106–107.
- ^ Daswani & Elbayadi 2021, p. 28.
- ^ Fowler 2016, p. 19.
- ^ Fowler 2016, pp. 18–19.
- ^ Daswani & Elbayadi 2021, pp. 31–32.
- ^ Solove & Hartzog 2022, pp. 69–70.
- ^ Daswani & Elbayadi 2021, pp. 7, 9–10.
- ^ Daswani & Elbayadi 2021, pp. 200–201.
- ^ Daswani & Elbayadi 2021, pp. 203–204.
- ^ Daswani & Elbayadi 2021, p. 205.
- ^ Daswani & Elbayadi 2021, pp. 206–207.
- ^ Fisher et al. 2024, Title page.
- ^ Fisher et al. 2024, p. 2.
- ^ Fowler 2016, p. 210.
- ^ a b Daswani & Elbayadi 2021, p. 217.
- ^ Daswani & Elbayadi 2021, pp. 215–216.
- ^ Tjoa et al. 2024, p. 14.
- ^ Lenhard 2022, p. 53.
- ^ Daswani & Elbayadi 2021, p. 218.
- ^ Daswani & Elbayadi 2021, pp. 218–219.
- ^ Daswani & Elbayadi 2021, pp. 314–315.
- ^ Tjoa et al. 2024, p. 68.
- ^ Lenhard 2022, p. 60.
- ^ Fowler 2016, p. 184.
- ^ Solove & Hartzog 2022, p. 146.
- ^ Tjoa et al. 2024, p. 69.
- ^ Crawley 2021, p. 39.
- ^ Fowler 2016, p. 64.
- ^ a b National Academies of Sciences, Engineering, and Medicine 2016, p. 25.
- ^ Fowler 2016, p. 4.
- ^ Crawley 2021, p. 97.
- ^ Fowler 2016, pp. 5, 32.
- ^ Fowler 2016, p. 86.
- ^ Fowler 2016, p. 94.
- ^ Fowler 2016, pp. 4–5.
- ^ Fowler 2016, pp. 120–122.
- ^ Fowler 2016, p. 115.
- ^ Fowler 2016, p. 116.
- ^ Fowler 2016, pp. 117–118.
- ^ Fowler 2016, p. 119.
- ^ Fowler 2016, p. 124.
- ^ Fowler 2016, pp. 81–82.
- ^ Fowler 2016, p. 83.
- ^ Fowler 2016, p. 128.
- ^ a b c d e National Academies of Sciences, Engineering, and Medicine 2016, p. 22.
- ^ Fowler 2016, p. 44.
- ^ a b Solove & Hartzog 2022, p. 58.
- ^ Fowler 2016, p. 5, 44.
- ^ a b c National Academies of Sciences, Engineering, and Medicine 2016, p. 13.
- ^ Fowler 2016, pp. 5–6.
- ^ Fowler 2016, p. 14.
- ^ Fowler 2016, pp. 12–13.
- ^ Fowler 2016, pp. 13–14.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, p. 27.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, pp. 30–31.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, p. 29.
- ^ Solove & Hartzog 2022, p. 56.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, pp. 27–29.
- ^ Makridis 2021, p. 1.
- ^ Fowler 2016, p. 22.
- ^ Fowler 2016, p. 41.
- ^ Sloan & Warner 2019, p. 104.
- ^ Makridis 2021, pp. 1, 7.
- ^ Sloan & Warner 2019, p. 64.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, pp. 8–10.
- ^ Fowler 2016, p. 21.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, p. 10.
- ^ a b Solove & Hartzog 2022, p. 10.
- ^ Solove & Hartzog 2022, p. 43.
- ^ Solove & Hartzog 2022, p. 44.
- ^ Solove & Hartzog 2022, p. 45.
- ^ Thomas 2023, pp. xxvii, xxix, xxxii–xxxiii, xxxiv.
- ^ National Academies of Sciences, Engineering, and Medicine 2016, p. 24.
- ^ Talesh 2018, p. 237.
- ^ Solove & Hartzog 2022, p. 48.
- ^ Solove & Hartzog 2022, pp. 48–49.
- ^ Solove & Hartzog 2022, p. 52.
- ^ a b Solove & Hartzog 2022, p. 53.
- ^ Fowler 2016, p. 5.
- ^ Fowler 2016, p. 222.
- ^ a b Solove & Hartzog 2022, pp. 55, 59.
- ^ a b Solove & Hartzog 2022, p. 55.
- ^ a b National Academies of Sciences, Engineering, and Medicine 2016, p. 23.
Sources
- Ablon, Lillian; Bogart, Andy (2017). Zero Days, Thousands of Nights: The Life and Times of Zero-Day Vulnerabilities and Their Exploits (PDF). Rand Corporation. ISBN 978-0-8330-9761-3.
- Crawley, Kim (2021). 8 Steps to Better Security: A Simple Cyber Resilience Guide for Business. John Wiley & Sons. ISBN 978-1-119-81124-4.
- ISBN 978-1-4842-6654-0.
- Davidoff, Sherri (2019). Data Breaches: Crisis and Opportunity. Addison-Wesley Professional. ISBN 978-0-13-450772-9.
- Fisher, William; Craft, R. Eugene; Ekstrom, Michael; Sexton, Julian; Sweetnam, John (2024). Data Confidentiality: Identifying and Protecting Assets Against Data Breaches (PDF) (Report). NIST Special Publications. National Institute of Standards and Technology.
- Fowler, Kevvie (2016). Data Breach Preparation and Response: Breaches are Certain, Impact is Not. Elsevier Science. ISBN 978-0-12-803451-4.
- Joerling, Jill (2010). "Data Breach Notification Laws: An Argument for a Comprehensive Federal Law to Protect Consumer Data". Washington University Journal of Law and Policy. 32: 467.
- Kaster, Sean D.; Ensign, Prescott C. (2023). "Privatized espionage: NSO Group Technologies and its Pegasus spyware". Thunderbird International Business Review. 65 (3): 355–364. .
- Lenhard, Thomas H. (2022). Data Security: Technical and Organizational Protection Measures against Data Loss and Computer Crime. Springer Nature. ISBN 978-3-658-35494-7.
- Lesemann, Dana J. (2010). "One More unto the Breach: An Analysis of Legal, Technological, and Policy Issues Involving Data Breach Notification Statutes". Akron Intellectual Property Journal. 4: 203.
- Makridis, Christos A (2021). "Do data breaches damage reputation? Evidence from 45 companies between 2002 and 2018". Journal of Cybersecurity. 7 (1). .
- ISBN 978-0-309-44505-4.)
{{cite book}}: CS1 maint: multiple names: authors list (link - Ntantogian, Christoforos; Malliaros, Stefanos; Xenakis, Christos (2019). "Evaluation of password hashing schemes in open source web platforms". Computers & Security. 84: 206–224. .
- Seaman, Jim (2020). PCI DSS: An Integrated Data Security Standard Guide. Apress. ISBN 978-1-4842-5808-8.
- Shukla, Samiksha; George, Jossy P.; Tiwari, Kapil; Kureethara, Joseph Varghese (2022). Data Ethics and Challenges. Springer Nature. ISBN 978-981-19-0752-4.
- Sloan, Robert H.; Warner, Richard (2019). Why Don't We Defend Better?: Data Breaches, Risk Management, and Public Policy. CRC Press. ISBN 978-1-351-12729-5.
- ISBN 978-0-19-094057-7.
- Talesh, Shauhin A. (2018). "Data Breach, Privacy, and Cyber Insurance: How Insurance Companies Act as "Compliance Managers" for Businesses". Law & Social Inquiry. 43 (2): 417–440. .
- Thomas, Liisa M. (2023). Thomas on Data Breach: A Practical Guide to Handling Data Breach Notifications Worldwide (PDF). ISBN 978-1-7319-5405-3.
- Tjoa, Simon; Gafić, Melisa; Kieseberg, Peter (2024). Cyber Resilience Fundamentals. Springer Nature. ISBN 978-3-031-52064-8.

