Signals intelligence in modern history
Before the development of
Signals intelligence became far more central to military (and to some extent diplomatic) intelligence generally with the mechanization of armies, development of
Origins

Electronic interception appeared as early as 1900, during the
The
As the Russian fleet prepared for conflict with Japan in 1904, the British ship
The Japanese also developed a wireless interception capability and succeeded in listening in to the then primitive Russian communications. Their successes emphasized the importance of this new source of military intelligence, and facilities for the exploitation of this information resource were established by all the major powers in the following years.
The
World War I
It was over the course of the War that the new method of intelligence collection - signals intelligence - reached maturity.[3] The British in particular built up great expertise in the newly emerging field of signals intelligence and codebreaking.
Failure to properly protect its communications fatally compromised the
France had significant signals intelligence in World War I. Commandant Cartier developed a system of wireless masts, including one on the Eiffel Tower to intercept German communications. The first such station was built as early as 1908, although was destroyed by flooding a few years afterward. In the early stages of the war, French intercepts were invaluable for military planning and provided the crucial intelligence to commander-in-chief Joseph Joffre that enabled him to carry out the successful counterattack against the Germans at the Marne in September 1914.
In 1918, French intercept personnel captured a message written in the new ADFGVX cipher, which was cryptanalyzed by Georges Painvin. This gave the Allies advance warning of the German 1918 Spring Offensive.
US communications monitoring of naval signals started in 1918, but was used first as an aid to naval and merchant navigation. In October 1918, just before the end of the war, the US Navy installed its first DF installation at its station at Bar Harbor, Maine, soon joined by five other Atlantic coast stations, and then a second group of 14 installations.[4] These stations, after the end of World War I, were not used immediately for intelligence. While there were 52 Navy medium wave (MF) DF stations in 1924, most of them had deteriorated.
By the start of the
On the declaration of war, one of Britain's first acts was to cut all German undersea cables. On the night of 3 August 1914, the cable ship Alert located and cut Germany's five trans-Atlantic cables, which ran down the English Channel. Soon after, the six cables running between Britain and Germany were cut.[5] This forced the Germans to use either a telegraph line that connected through the British network and could be tapped, or through radio which the British could then intercept. The destruction of more secure wired communications, to improve the intelligence take, has been a regular practice since then. While one side may be able to jam the other's radio communications, the intelligence value of poorly secured radio may be so high that there is a deliberate decision not to interfere with enemy transmissions.
Although Britain could now intercept German communications, codes and ciphers were used to hide the meaning of the messages. Neither Britain nor Germany had any established organisations to decode and interpret the messages at the start of the war - the Royal Navy had only one wireless station for intercepting messages, at Stockton-on-Tees.[6][7]
However, installations belonging to the Post Office and the

A similar organisation had begun in the Military Intelligence department of the
In a stroke of luck, the SKM codebook was obtained from the German Light cruiser
A second important code - the Handelsverkehrsbuch (HVB) codebook used by the German navy - was captured at the very start of the war from the German-Australian steamer Hobart, seized off Port Philip Heads near Melbourne on 11 August 1914. The code was used particularly by light forces such as patrol boats, and for routine matters such as leaving and entering harbour. The code was used by U-boats, but with a more complex key. A third codebook was recovered following the sinking of German destroyer SMS S119 in a battle off Texel island. It contained a copy of the Verkehrsbuch (VB) codebook, intended for use in cables sent overseas to warships and naval attachés, embassies and consulates. Its greatest importance during the war was that it allowed access to communications between naval attachés in Berlin, Madrid, Washington, Buenos Aires, Peking, and Constantinople.[6]
The German fleet was in the habit each day of wirelessing the exact position of each ship and giving regular position reports when at sea. It was possible to build up a precise picture of the normal operation of the High Seas Fleet, indeed to infer from the routes they chose where defensive minefields had been place and where it was safe for ships to operate. Whenever a change to the normal pattern was seen, it immediately signalled that some operation was about to take place and a warning could be given. Detailed information about submarine movements was also available.[6]
Direction finding
The use of radio receiving equipment to pinpoint the location of the transmitter was also developed during the war. Captain
Room 40 had very accurate information on the positions of German ships, but the Admiralty priority remained to keep the existence of this knowledge secret. From June 1915 the regular intelligence reports of ship positions ceased to be passed to all flag officers, but only to Admiral Jellicoe himself. Similarly, he was the only person to receive accurate charts of German minefields prepared from Room 40 information. No attempts were made by the German fleet to restrict its use of wireless until 1917, and then only in response to perceived British use of direction finding, not because it believed messages were being decoded.[6]
It became increasingly clear, that as important as the decrypts were, it was of equal importance to accurately analyse the information provided. An illustration of this was provided by someone at the Admiralty who knew a little too much detail about SIGINT without fully understanding it. He asked the analysts where call sign "DK" was located, which was that used by the German commander when in harbour.
Jellicoe's faith in cryptographic intelligence was also shaken by a decrypted report that placed the German cruiser SMS Regensburg near him, during the Battle of Jutland. It turned out that the navigator on the Ravensburg was off by 10 miles (16 km) in his position calculation. During Jutland, there was limited use of direction finding on fleet vessels, but most information came from shore stations. A whole string of messages were intercepted during the night indicating with high reliability how the German fleet intended to make good its escape, but the brief summary which was passed to Jellicoe failed to convince him of its accuracy in light of the other failures during the day.
Zimmermann Telegram & Other Successes
Room 40 played an important role in several naval engagements during the war, notably in detecting major German sorties into the North Sea. The battle of Dogger Bank was won in no small part due to the intercepts that allowed the Navy to position its ships in the right place. "Warned of a new German raid [on England] on the night of 23–24 January, by radio intercepts, [Admiral Sir David] Beatty’s force made a rendezvous off the Dogger Bank... The outnumbered Germans turned in flight. ... the Kaiser, fearful of losing capital ships, ordered his navy to avoid all further risks."[9]
It played a vital role in subsequent naval clashes, including at the
In the telegram's plaintext, Nigel de Grey and William Montgomery learned of the German Foreign Minister Arthur Zimmermann's offer to Mexico of United States' territories of Arizona, New Mexico, and Texas as an enticement to join the war as a German ally. The telegram was passed to the U.S. by Captain Hall, and a scheme was devised (involving a still unknown agent in Mexico and a burglary) to conceal how its plaintext had become available and also how the U.S. had gained possession of a copy. The telegram was made public by the United States, which declared war on Germany on 6 April 1917, entering the war on the Allied side.
Interwar period
With the importance of interception and decryption firmly established by the wartime experience, countries established permanent agencies dedicated to this task in the interwar period.
These agencies carried out substantial SIGINT work between the World Wars, although the secrecy surrounding it was extreme. While the work carried out was primarily COMINT,
United Kingdom
In 1919, the British Cabinet's Secret Service Committee, chaired by
By 1922, the main focus of GC&CS was on diplomatic traffic, with "no service traffic ever worth circulating"
In the 1920s, GC&CS was successfully reading Soviet Union diplomatic ciphers. However, in May 1927, during a row over clandestine Soviet support for the General Strike and the distribution of subversive propaganda, Prime Minister Stanley Baldwin made details from the decrypts public.[16]
By 1940, GC&CS was working on the diplomatic codes and ciphers of 26 countries, tackling over 150 diplomatic cryptosystems.[17]
Germany
From the mid-twenties, German Military Intelligence Abwehr began intercepting and cryptanalyzing diplomatic traffic. Under Hermann Göring, the Nazi Research Bureau (Forschungsamt or "FA") had units for intercepting domestic and international communications. The FA was penetrated by a French spy in the 1930s, but the traffic grew to a point that it could not easily be forwarded.
In addition to intercept stations in Germany, the FA established an intercept station in Berne, Switzerland. German code breaking penetrated most cryptosystems, other than the UK and US.[1] German Condor Legion personnel in the Spanish Civil War ran COMINT against their opponents.
United States
The US Cipher Bureau was established in 1919 and achieved some success at the Washington Naval Conference in 1921, through cryptanalysis by Herbert Yardley. Secretary of War Henry L. Stimson closed the US Cipher Bureau in 1929 with the words "Gentlemen do not read each other's mail."
Luckily for US COMINT, the Army offered a home to
The American Sigint effort began in the early 1930s with mounting tensions with the Japanese. The
By December 1940, the Navy's communication organization, OP-20-G, had used HF/DF on German surface vessels and submarines. Training continued and cooperation with the British began. In April 1941, the British gave the US Navy a sample of their best HF/DF set from Marconi.
World War II
The use of SIGINT had even greater implications during
A true world war, SIGINT still tended to be separate in the various theaters. Communications security, on the part of the Allies, was more centralized. From the Allied perspective, the critical theater-level perspectives were the Ultra SIGINT against the Germans in the European theater (including the
The entire German system of high command suffered from
Germany enjoyed some SIGINT success against the Allies, especially with the Merchant Code and, early in the war, reading American attaché traffic. German air intelligence, during the Battle of Britain, suffered from the structural problem that subordinated intelligence to operations. Operations officers often made conclusions that best fit their plans, rather than fitting conclusions to information.[19]
In contrast, British air intelligence was systematic, from the highest-level, most sensitive Ultra to significant intelligence product from traffic analysis and cryptanalysis of low-level systems. Fortunately for the British, German aircraft communications discipline was poor, and the Germans rarely changed call signs, allowing the British to draw accurate inferences about the air order of battle.
Japan was the least effective of the major powers in SIGINT. In addition to the official Allies and Axis battle of signals, there was a growing interest in Soviet espionage communications, which continued after the war.
British SIGINT
The British
Commander Alastair Denniston was operational head of GC&CS. Key GC&CS cryptanalysts who moved from London to Bletchley Park included John Tiltman, Dillwyn "Dilly" Knox, Josh Cooper, and Nigel de Grey. These people had a variety of backgrounds – linguists, chess champions, and crossword experts were common, and in Knox's case papyrology.[18][21] In one 1941 recruiting stratagem The Daily Telegraph was asked to organise a crossword competition, after which promising contestants were discreetly approached about "a particular type of work as a contribution to the war effort".[22]
Denniston recognised, however, that the enemy's use of electromechanical cipher machines meant that formally trained mathematicians would be needed as well; Oxford's
Properly used, the German Enigma and Lorenz ciphers should have been virtually unbreakable, but flaws in German cryptographic procedures, and poor discipline among the personnel carrying them out, created vulnerabilities which made Bletchley's attacks just barely feasible. These vulnerabilities, however, could have been remedied by relatively simple improvements in enemy procedures,[30] and such changes would certainly have been implemented had Germany any hint of Bletchley's success. Thus the intelligence Bletchley produced was considered wartime Britain's "Ultra secret" – higher even than the normally highest classification Most Secret [31] – and security was paramount.
Initially, a wireless room was established at Bletchley Park. It was set up in the mansion's water tower under the code name "Station X", a term now sometimes applied to the codebreaking efforts at Bletchley as a whole.[32] Due to the long radio aerials stretching from the wireless room, the radio station was moved from Bletchley Park to nearby Whaddon Hall to avoid drawing attention to the site.[33]
Subsequently, other listening stations – the
Bletchley's work was essential to defeating the
German codes

Most German messages decrypted at Bletchley were produced by one or another version of the Enigma cipher machine, but an important minority were produced by the even more complicated twelve-rotor Lorenz SZ42 on-line teleprinter cipher machine.
Five weeks before the outbreak of war, in Warsaw, Poland's
The bombe was an electromechanical device whose function was to discover some of the daily settings of the Enigma machines on the various German military networks.[18][38][39] Its pioneering design was developed by Alan Turing (with an important contribution from Gordon Welchman) and the machine was engineered by Harold 'Doc' Keen of the British Tabulating Machine Company. Each machine was about 7 feet (2.1 m) high and wide, 2 feet (0.61 m) deep and weighed about a ton.[40]
At its peak, GC&CS was reading approximately 4,000 messages per day.[41] As a hedge against enemy attack[42] most bombes were dispersed to installations at Adstock and Wavendon (both later supplanted by installations at Stanmore and Eastcote), and Gayhurst.[43][44]
SIGINT played a most important role for the

It is unclear why the German submarine command believed that frequent radio communications were not a hazard to their boats, although they seemed confident in the security of their Enigma ciphers, both in the initial three-rotor and subsequent four-rotor versions (known as Triton to the Germans and Shark to the Allies). There was an apparent, mutually reinforcing belief that wolfpack attacks by groups of submarines were much more deadly than individual operations, and confidence the communications were secure. Arguably, the Germans underestimated HF/DF even more than they did British cryptanalysis.[45] Apparently, the Germans did not realize that the Allies were not limited to slow, manually operated direction finders, and also underestimated the number of direction finders at sea. On the other hand, the introduction of a new secure communication system would have interrupted submarine operations for a long time since a gradual shift to a new system was out of the question.
The Lorenz messages were codenamed Tunny at Bletchley Park. They were only sent in quantity from mid-1942. The Tunny networks were used for high-level messages between German High Command and field commanders. With the help of German operator errors, the cryptanalysts in the Testery (named after Ralph Tester, its head) worked out the logical structure of the machine despite not knowing its physical form. They devised automatic machinery to help with decryption, which culminated in Colossus, the world's first programmable digital electronic computer. This was designed and built by Tommy Flowers and his team at the Post Office Research Station at Dollis Hill. The first was delivered to Bletchley Park in December 1943 and commissioned the following February. Enhancements were developed for the Mark 2 Colossus, the first of which was working at Bletchley Park on the morning of D-day in June. Flowers then produced one Colossus a month for the rest of the war, making a total of ten with an eleventh part-built. The machines were operated mainly by Wrens in a section named the Newmanry after its head Max Newman.
The "Radio Security Service" was established by MI8 in 1939 to control a network of Direction Finding and intercept stations to locate illicit transmissions coming from German spies in Britain. This service was soon intercepting a network of German Secret Service transmissions across Europe. Successful decryption was achieved at an early stage with the help of codes obtained from the British XX (Double Cross) System that "turned" German agents and used them to misdirect German intelligence. The combination of double agents and extensive penetration of German intelligence transmissions facilitated a series of highly successful strategic deception programmes throughout WWII.
Italian codes
Breakthroughs were also made with Italian signals. During the
On entering World War II in June 1940, the Italians were using book codes for most of their military messages. The exception was the
Japanese codes

An outpost of the Government Code and Cypher School was set up in Hong Kong in 1935, the Far East Combined Bureau (FECB), to study Japanese signals. The FECB naval staff moved in 1940 to Singapore, then Colombo, Ceylon, then Kilindini, Mombasa, Kenya. They succeeded in deciphering Japanese codes with a mixture of skill and good fortune.[53] The Army and Air Force staff went from Singapore to the Wireless Experimental Centre at Delhi, India.
In early 1942, a six-month crash course in Japanese, for 20 undergraduates from Oxford and Cambridge, was started by the Inter-Services Special Intelligence School in Bedford, in a building across from the main Post Office. This course was repeated every six months until war's end. Most of those completing these courses worked on decoding Japanese naval messages in Hut 7, under John Tiltman. By mid-1945 well over 100 personnel were involved with this operation, which co-operated closely with the FECB and the US Signal intelligence Service at Arlington Hall, Virginia. Because of these joint efforts, by August of that year the Japanese merchant navy was suffering 90% losses at sea.[citation needed] In 1999, Michael Smith wrote that: "Only now are the British codebreakers (like John Tiltman, Hugh Foss, and Eric Nave) beginning to receive the recognition they deserve for breaking Japanese codes and cyphers".[54]
US SIGINT
During the Second World War, the
After the Normandy landings, Army SIGINT units accompanied major units, with traffic analysis as - or more - important than the tightly compartmented cryptanalytic information. General Bradley's Army Group, created on August 1, 1944, had SIGINT including access to Ultra. Patton's subordinate Third Army had a double-sized Signal Radio Intelligence Company attached to his headquarters, and two regular companies were assigned to the XV and VIII Corps.[56]
The US Navy used SIGINT in its anti-submarine warfare, using shore or ship-based SIGINT to vectored long-range patrol aircraft to U-boats.[57]
Allied cooperation in the
At first, Central Bureau was made up of 50% American, 25%
Until Central Bureau received replacement data processing equipment for that which was lost in the Philippines, as of January 1942, U.S. Navy stations in Hawaii (Hypo), Corregidor (Cast) and OP-20-G (Washington) decrypted Japanese traffic well before the U.S. Army or Central Bureau in Australia. Cast, of course, closed with the evacuation of SIGINT personnel from the Philippines. Central Bureau broke into two significant Japanese Army cryptosystems in mid-1943.
Japanese codes
The
Traffic analysts began tracking Japanese units in near real time. A critical result was the identification of the movement, by sea, of two Japanese infantry divisions from Shanghai to New Guinea. Their convoy was intercepted by US submarines, causing almost complete destruction of these units.[56]
Army units in the Pacific included the US 978th Signal Company based at the Allied Intelligence Bureau's secret "Camp X", near
US Navy strategic stations targeted against Japanese sources at the outbreak of the war, included
Perhaps most dramatically, intercepts of Japanese naval communications
The
They learned the Japanese air-to-ground network was
Two Japanese naval stations were in the Army net, and it handled both operations and ferrying of aircraft for staging new operations. Traffic analysis of still-encrypted traffic helped MacArthur predict Japanese moves as the Fil-American forces retreated in Bataan.An Australian-American intercept station was later built at Townsville, Queensland. US Air Force Far East, and its subordinate 5th Air Force, took control of the 126th in June 1943. The 126th was eventually placed under operational control of U.S. Air Force Far East in June 1943 to support 5th Air Force. Interception and traffic analysis from the company supported the attack into Dutch New Guinea in 1944.[56]
Cold War
After the end of World War II, the Western allies began a rapid drawdown. At the end of WWII, the US still had a COMINT organization split between the Army and Navy. [61] A 1946 plan listed Russia, China, and a [redacted] country as high-priority targets.
From 1943 to 1980, the Venona project, principally a US activity with support from Australia and the UK, recovered information, some tantalizingly only in part, from Soviet espionage traffic. While the Soviets had originally used theoretically unbreakable one-time pads for the traffic, some of their operations violated communications security rules and reused some of the pads. This reuse caused the vulnerability that was exploited.
Venona gave substantial information on the scope of Soviet espionage against the West, but critics claim some messages have been interpreted incorrectly, or are even false. Part of the problem is that certain persons, even in the encrypted traffic, were identified only by code names such as "Quantum". Quantum was a source on US nuclear weapons, and is often considered to be Julius Rosenberg. The name, however, could refer to any of a number of spies.
US Tactical SIGINT
After the
Recognizing that national sources simply might not have information on a given environment, or that they might not make it available to warfighters, Lieutenant General Gray directed that a SIGINT function be created that could work with the elite Force Reconnaissance Marines who search out potential enemies. At first, neither the Force Reconnaissance nor Radio Battalion commanders thought this was viable, but had orders to follow.
Initially, they attached a single Radio Battalion Marine, with an AN/GRR-8 intercept receiver, to a Force Reconnaissance team during an exercise. A respected Radio Marine, Corporal Kyle O'Malley was sent to the team, without any guidance for what he was to do. The exercise did not demonstrate that a one-man attachment, not Force Recon qualified, was useful.
In 1984, Captain E.L. Gillespie, assigned to the Joint Special Operations Command, was alerted that he was to report to 2nd Radio Battalion, to develop a concept of operations for integrating SIGINT capabilities with Force Recon, using his joint service experience with special operations. Again, the immediate commanders were not enthusiastic.
Nevertheless, a mission statement was drafted: "To conduct limited communications intelligence and specified electronic warfare operations in support of Force Reconnaissance operations during advance force or special operations missions." It was decided that a 6-man SIGINT team, with long/short range independent communications and SIGINT/EW equipment, was the minimum practical unit. It was not practical to attach this to the smallest 4-man Force Recon team.
General Gray directed that the unit would be called a
From 1986 on, RRTs accompanied MEU(SOC) deployments. Their first combat role was in Operation Earnest Will, then Operation Praying Mantis, followed by participation in the 1989 United States invasion of Panama
Recent history
Threat from terrorism
Terrorism from foreign groups became an increasingly major concern beginning in the late 20th century, as seen with the
- Inherently low probability of intercept/detection (LPI/LPD) because off-the-shelf radios can be frequency agile, spread spectrum, and transmit in bursts.
- Additional frequencies, not normally monitored, can be used. These include and higher frequencies for short-range communications
- Extensive use of telephones, almost always digital. Cellular and satellite telephones, while wireless, are challenging to intercept, as is Voice over IP (VoIP)
- Commercial strong encryption for voice and data
- "Extremely wide variety and complexity of potential targets, creating a "needle in the haystack" problem"[63]
As a result of the 9/11 attacks, intensification of US intelligence efforts, domestic and foreign, were to be expected. A key question, of course, was whether US intelligence could have prevented or mitigated the attacks, and how it might prevent future attacks. There is a continuing clash between advocates for civil liberties and those who assert that their loss is an agreeable exchange for enhanced safety.[citation needed]
Another possibility is the use of software tools that do high-performance deep packet inspection. According to the marketing VP of Narus, "Narus has little control over how its products are used after they're sold. For example, although its lawful-intercept application has a sophisticated system for making sure the surveillance complies with the terms of a warrant, it's up to the operator whether to type those terms into the system...
"That legal eavesdropping application was launched in February 2005, well after whistle-blower Klein allegedly learned that AT&T was installing Narus boxes in secure, NSA-controlled rooms in switching centers around the country. But that doesn't mean the government couldn't write its own code to do the dirty work. Narus even offers software-development kits to customers ".[64] The same type of tools with legitimate ISP security applications also have COMINT interception and analysis capability.
Former AT&T technician Mark Klein, who revealed AT&T was giving NSA access, said in a statement, said a Narus STA 6400 was in the NSA room to which AT&T allegedly copied traffic. The Narus device was "known to be used particularly by government intelligence agencies because of its ability to sift through large amounts of data looking for preprogrammed targets."[64]
European Space Systems cooperation
France launched Helios 1A as a military photo-reconnaissance satellite on 7 July 1995.[65] The Cerise (satellite) SIGINT technology demonstrator also was launched in 1995. A radio propagation experiment, S80-T, was launched in 1992, as a predecessor of the ELINT experiments. Clementine, the second-generation ELINT technology demonstrator, was launched in 1999.
Financial pressures in 1994-1995 caused France to seek Spanish and Italian cooperation for
The same launcher carried French and Spanish scientific satellites and four
Germany launched their first reconnaissance satellite system,
The joint French-Italian Orfeo Programme, a dual-use civilian and military satellite system,[71] launched its first satellite on June 8, 2007.[72] Italy is developing the Cosmo-Skymed X-band polarimetric SAR, to fly on two of the satellites. The other two will have complementary French electro-optical payloads. The second Orfeo is scheduled to launch in early 2008.
See also
References
- ^ a b Lee, Bartholomew. "Radio Spies – Episodes in the Ether Wars" (PDF). Retrieved 8 October 2007.
- ^ Report from HMS Diana on Russian Signals intercepted at Suez, 28 January 1904, Naval library, Ministry of Defence, London.
- ^ Douglas L. Wheeler. "A Guide to the History of Intelligence 1800-1918" (PDF). Journal of U.S. Intelligence Studies.
- ^ Clancey, Patrick, "Battle of the Atlantic, Volume I. Allied Communications Intelligence, December 1942 to May 1945 [SRH-005]", HyperWar: A Hypertext History of the Second World War, HyperWar Foundation, retrieved 15 October 2007
- S2CID 201749182.
- ^ ISBN 0-241-10864-0.
- ^ "Marley Close, Stockton-on-Tees: Intelligence HQ for the Royal Navy". BBC. 1 November 2015. Retrieved 27 May 2016.
- ^ Kahn 1996
- ^ Livesey, Anthony, Historical Atlas of World War One, Holt; New York, 1994 p. 64
- ^ "Code Breaking and Wireless Intercepts".
- ^ ASIN B002ALSXTC.
- ISBN 0-304-36545-9.
- ISBN 978-0593049105.
- ISBN 978-0-7110-3408-2.
- .
- ^ Aldrich, 2010, p. 18
- ^ David Alvarez, GC&CS and American Diplomatic Cryptanalysis
- ^ ISBN 978-0-684-85932-3
- ^ Lund, Earle, The Battle of Britain: A German Perspective; Addendum, Luftwaffe Air Intelligence During the Battle of Britain, retrieved 6 October 2007
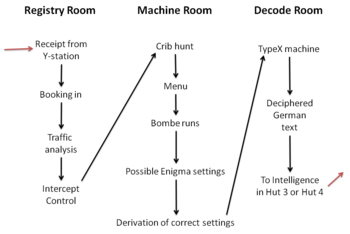
- ^ Sale, Tony, Information flow from German ciphers to Intelligence to Allied commanders., retrieved 30 June 2011
- ISBN 978-0-7509-3362-9
- ^ McKay, Sinclair (26 August 2010), "Telegraph crossword: Cracking hobby won the day – The boffins of Bletchley cut their teeth on the Telegraph crossword", The Telegraph, archived from the original on 31 August 2010
- ^ Twinn, Peter (1993), The Abwehr Enigma
- ISBN 978-0099116417
- ^ Taunt, Derek, Hut 6: 1941-1945, p. 101
- Good, Jack, Enigma and Fish, p. 154
- ^ Tutte, William T. (2006), My Work at Bletchley Park Appendix 4
- ^ Burman, Annie. "Gendering decryption – decrypting gender The gender discourse of labour at Bletchley Park 1939–1945" (PDF). Retrieved 27 October 2013.
- ^ "Women Codebreakers". Bletchley Park Research. Retrieved 3 November 2013.
- ^ a b Milner-Barry 1993, p. 92
- ^ Hinsley & Stripp 1993, p. vii
- ^ Watson, Bob (1993), Appendix: How the Bletchley Park buildings took shape, p. 307
- ^ Smith, Michael; Butters, Lindsey (2007) [2001], The Secrets of Bletchley Park: Official Souvenir Guide, Bletchley Park Trust, p. 10
- ^ Gross, Kuno, Michael Rolke and András Zboray, Operation SALAM - László Almásy’s most daring Mission in the Desert War, Belleville, München, 2013
- ISBN 0-06-014678-8
- ^ Hinsley, Sir Harry (1996) [1993], The Influence of ULTRA in the Second World War (PDF), retrieved 23 July 2012
- ^ Twinn, Peter (1993), The Abwehr Enigma in Hinsley & Stripp 1993, p. 127
- ISBN 978-0-297-84251-4
- ^ Carter, Frank (2004), From Bombe Stops to Enigma Keys (PDF), Bletchley Park Codes Centre, archived from the original (PDF) on 8 January 2010, retrieved 31 March 2010
- ^ Ellsbury, Graham (1988), "2. Description of the Bombe", The Turing Bombe: What it was and how it worked, retrieved 1 May 2010
- ISSN 1177-1380
- ^ "Outstations from the Park", Bletchley Park Jewels, archived from the original on 13 December 2009, retrieved 16 April 2010
- ^ Toms, Susan (2005), Enigma and the Eastcote connection, archived from the original on 4 December 2008, retrieved 16 April 2010
- ^ Welchman 1997, p. 141
- ^ Barratt, John (2002), "Enigma and Ultra - the Cypher War", Military History Online.com, Barratt 2002
- ^ Grey 2012, pp. 132–3
- ^ Batey, Mavis (2011), Breaking Italian Naval Enigma, p. 81 in Erskine & Smith 2011, pp. 79–92
- ^ Hinsley, Sir Harry (1996) [1993], The Influence of ULTRA in the Second World War, archived from the original on 6 July 2012, retrieved 23 July 2012 Transcript of a lecture given on Tuesday 19 October 1993 at Cambridge University
- ^ Dakin, Alec Naylor (1993), The Z Watch in Hut 4, Part I in Hinsley & Stripp 1993, pp. 50–56
- ^ Wilkinson, Patrick (1993), Italian naval ciphers in Hinsley & Stripp 1993, pp. 61–67
- ^ "July 1941". Bletchley Park. Archived from the original on 20 July 2011. Retrieved 23 February 2013.
- ^ Anna Pukas (28 April 2012). "Our family war heroes". Daily Express. Archived from the original on 14 January 2016.
{{cite web}}: CS1 maint: bot: original URL status unknown (link) - ^ Smith, Michael. "Mombasa was base for high-level UK espionage operation". coastweek.com. Coastweek. Retrieved 20 June 2013.
- ^ Smith 2001, pp. 127–51
- ^ Thomas L. Burns (1990), The Origins of the National Security Agency, 1940-1952, National Security Agency, archived from the original on 3 January 2008
- ^ a b c d Joseph, Browne (2006), "Radio-traffic analysis' contributions", Army Communicator, archived from the original on 13 June 2007, retrieved 15 October 2007
- ^ Cote, Owen R. Jr. (March 2000), The Third Battle: Innovation in the U.S. Navy's Silent Cold War Struggle with Soviet Submarines, MIT Security Studies Program, Cote 200, archived from the original on 10 April 2006, retrieved 4 November 2020
- ^ Dunn, Peter (9 April 2000), Central Bureau in Australia during World War II: A Research and Control Centre for the Interception and cryptanalyzing of Japanese intelligence, retrieved 16 October 2006
- ^ Dunn, Peter (2003), 978th Signal Service Company Based at Camp Tabragalba, near Beaudesert, QLB during World War II, retrieved 5 October 2007
- ^ National Security Agency, Battle of Midway, NSA Midway, archived from the original on 21 August 2007, retrieved 2 October 2007
- ^ Hanyok, Robert J. (2002), "Chapter 1 - Le Grand Nombre Des Rues Sans Joie: [Deleted] and the Franco-Vietnamese War, 1950-1954", Spartans in Darkness: American SIGINT and the Indochina War, 1945-1975 (PDF), Center for Cryptologic History, National Security Agency
- ^ Jeremy Choate (2007), History and Mission [2nd Marine Radio Battalion, Radio Reconnaissance Platoon], 2RRP, archived from the original on 25 June 2007, retrieved 19 October 2007
- Gray, Alfred M. (Winter 1989–1990), "Global Intelligence Challenges in the 1990s"(PDF), American Intelligence Journal: 37–41, retrieved 8 October 2007
- ^ a b Singel, Ryan (4 July 2006), "Whistle-Blower Outs NSA Spy Room", Wired, ATTWired, archived from the original on 30 April 2008, retrieved 8 October 2007
- ^ Federation of American Scientists, Helios, FAS Helios, retrieved 19 October 2007
- ^ Mark Urban, UK Eyes Alpha: the Inside Story of British Intelligence. Chapter 5: Zircon, Urban 1996, retrieved 19 October 2007
- ^ Tariq Malik (18 December 2004), Ariane 5 Successfully Orbits France's Helios 2A Satellite, Space.com, Malik 2004, retrieved 19 October 2007
- ^ Jonathan McDowell (25 December 2004), Jonathan's Space Report No. 541: Helios 2, McDowell 2004, archived from the original on 22 July 2007, retrieved 19 October 2007
- ^ Space Daily (3 July 2005), "ESSAIM, Micro-Satellites In Formation", Space Daily, ESSAIM 2005, retrieved 19 October 2007
- ^ [1] Spaceflight now - Radar reconnaissance spacecraft launched
- ^ Deagel.com (19 October 2007), Successful Launch Second German Sar-Lupe Observation Satellite, Deagel 2007, retrieved 19 October 2007
- ^ William Atkins (9 June 2007), "Italian COSMO-SkyMed satellite launched to study world's weather", ITwire, Atkins 2007, retrieved 19 October 2007
Bibliography
- Aldrich, R. J. (2010), GCHQ: The Uncensored Story of Britain's Most Secret Intelligence Agency, London: HarperCollins Press, ISBN 978-0-00-727847-3
- Alvarez, David (2001), "Most Helpful and Cooperative: GC&CS and the Development of American Diplomatic Cryptanalysis, 1941-1942", in Smith, Michael; Erskine, Ralph (eds.), Action This Day: Bletchley Park from the Breaking of the Enigma Code to the Birth of the Modern Computer, Bantam Press, ISBN 978-0593049105
- Budiansky, Stephen (2000), Battle of wits: The Complete Story of Codebreaking in World War II, Free Press, pp. 176–179, ISBN 978-0684859323
- Holmes, W. J. (1979), Double-edged Secrets: U.S. Naval Intelligence Operations in the Pacific During World War II, Annapolis, Maryland: Blue Jacket Books/Naval Institute Press, ISBN 1-55750-324-9
- ISBN 0684831309
- Lee, Bartholomew (2006), Radio Spies -- Episodes in the Ether Wars (PDF), retrieved 8 October 2007
- Parker, Frederick D., A Priceless Advantage: U.S. Navy Communications Intelligence and the Battles of Coral Sea, Midway, and the Aleutians, National Security Agency, Central Security Service, retrieved 20 November 2006
- Prados, John (1995), Combined Fleet Decoded: The Secret History of American Intelligence and the Japanese Navy in World War II, New York: Random House, ISBN 0-679-43701-0
