Common Scrambling Algorithm
The Common Scrambling Algorithm (CSA) is the
CSA was specified by
History
CSA was largely kept secret until 2002. The patent papers gave some hints, but important details, like the layout of the so-called S-boxes, remained secret. Without these, free implementations of the algorithm was not possible. Initially, CSA was to remain implemented in hardware only, making it difficult to reverse engineer existing implementations.
In 2002 FreeDec was released, implementing CSA in software. Though released as binary only, disassembly revealed the missing details and allowed reimplementation of the algorithm in higher-level programming languages.
With CSA now publicly known in its entirety,
Description of the cipher
The CSA algorithm is composed of two distinct ciphers: a block cipher and a stream cipher.
When used in encryption mode the data are first encrypted using the 64-bit block cipher in
Block cipher
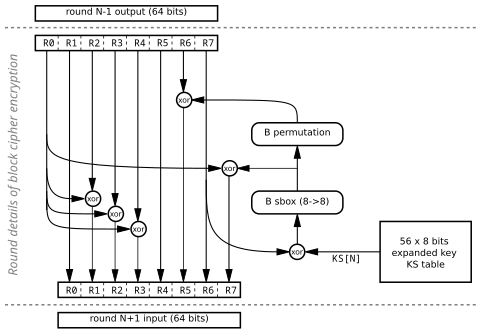
The block cipher process 64-bit blocks in 56 rounds. It uses 8 bits from an expanded key on each round.
Stream cipher
The first 32 round of the stream cipher are used for initialization and do not generate any output. The first 64 bits of data are used as initialization vector during this phase and are left unchanged. The stream cipher then generates 2 bits of pseudo-random stream on each round which are xored starting at bit 64 of the packet.
Weaknesses
Were CSA to be broken, encrypted DVB transmissions would be decipherable, which would compromise paid digital television services, as DVB has been standardised for digital terrestrial television in Europe and elsewhere, and is used by many satellite television providers.
Most attacks on the pay-TV system have not targeted CSA itself, but instead the various key exchange systems responsible for generating the CSA keys (Conax, Irdeto, Nagravision, VideoGuard, etc.), either by reverse-engineering and breaking the algorithms altogether, or by intercepting the keys in real-time as they are generated on a legitimate decoder, and then distributing them to others (so-called card sharing).
Software implementations and bit slicing
The stream cipher part of CSA is prone to bit slicing, a software implementation technique which allows decryption of many blocks, or the same block with many different keys, at the same time. This significantly speeds up a brute force search implemented in software, although the factor is too low for a practical real-time attack.
The block cipher part is harder to bit slice, as the
Both techniques are used in libdvbcsa, a free implementation of CSA.
Cryptanalysis
Cryptanalysis is made more difficult as most data is protected both by the block and the stream cipher. Adaption codes can result in packets with some data protected by only the block cipher or the stream cipher.[2]
Brute force approach
While the CSA algorithm uses 64-bit keys, most of the time, only 48 bits of the key are unknown, since bytes 3 and 7 are used as parity bytes in CA systems, and may be easily recalculated. This allows for possible
Known-plaintext attack
In 2011, a group of German researchers released an attack
This differs from the brute-force attack examples already mentioned, in that the plain-text contents of the entire cell is known before the attack, not just parts of a block, which enables the ahead-of-time computation of the rainbow table.
Fault attack
In 2004, a fault attack[4] was published on the block cipher. The basic idea was to introduce a few deliberate faults in the intermediate calculations, making it possible to deduce the last eight round keys. From this, the final key can be computed.
While very few faults are needed (on average two or three per round key recovered), fault attacks are usually impractical to carry out, in that it requires the ability to change bits at will inside the hardware of a decoder that already has the key in question.
References
- ^ Farncombe Consulting Group (2009). "Towards a Replacement for the DVB Common Scrambling Algorithm" (PDF) (white paper). Basingstoke. Archived from the original (PDF) on 2010-07-05. Retrieved 2012-11-20.
- ISBN 978-0-387-24486-0.
- ISBN 978-3-642-34158-8.
- ^ Wirt, Kai (November 2003). "Fault attack on the DVB Common Scrambling Algorithm (Report 2004/289)". Cryptology ePrint Archive.