Search results
Appearance
There is a page named "Trusted Information Systems" on Wikipedia
- Trusted Information Systems (TIS) was a computer security research and development company during the 1980s and 1990s, performing computer and communications...7 KB (666 words) - 09:47, 30 May 2024
- from a trusted system. The dedication of significant system engineering toward minimizing the complexity (not size, as often cited) of the trusted computing...17 KB (2,358 words) - 22:49, 30 July 2023
- In information system and information technology, trust management is an abstract system that processes symbolic representations of social trust, usually...5 KB (700 words) - 17:39, 17 November 2023
- geographic information systems, also abbreviated GIS, is the most common term for the industry and profession concerned with these systems. It is roughly...99 KB (13,021 words) - 02:25, 20 June 2024
- Automated Trusted Information Exchange (ATIX) is a computer database containing homeland security and terrorist threat information, which is part of the...1 KB (108 words) - 06:00, 17 June 2024
- 4+) Trusted Solaris Trusted UNICOS 8.0 (Rated B1) XTS-400 (Rated EAL5+) IBM VM (SP, BSE, HPO, XA, ESA, etc.) with RACF Examples of operating systems that...4 KB (406 words) - 08:23, 27 March 2023
- Mitretek Systems and EDS. While working at Trusted Information Systems, Bell presented two papers, "Lattices, Policies and Implementations", and "Trusted Xenix...8 KB (713 words) - 10:38, 19 April 2024
- Trusted XENIX)to the Xenix system. Trusted Xenix was a variant initially developed by IBM, under the name Secure XENIX; later versions, under the Trusted Xenix name,...31 KB (3,136 words) - 19:40, 7 June 2024
- techniques – Information security management systems – Overview and vocabulary. ISO/IEC. Committee on National Security Systems: National Information Assurance...191 KB (22,107 words) - 17:05, 23 June 2024
- Trusted Computing (TC) is a technology developed and promoted by the Trusted Computing Group. The term is taken from the field of trusted systems and...42 KB (5,183 words) - 18:30, 6 June 2024
- Certified in Risk and Information Systems Control)association focused on IT (information technology) governance. On its IRS filings, it is known as the Information Systems Audit and Control Association...14 KB (1,042 words) - 08:30, 20 May 2024Trusted Computer System Evaluation Criteria (TCSEC) is a United States Government Department of Defense (DoD) standard that sets basic requirements for...18 KB (2,101 words) - 21:38, 25 February 2024(category Unix file system technology)Mach-derived Distributed Trusted Operating System, as well as on Trusted Mach, a research project from Trusted Information Systems that had an influence...31 KB (3,387 words) - 20:42, 22 June 2024
- operating system. Assuring that an authentic operating system starts in a trusted environment, which can then be considered trusted. Provision of a trusted operating...12 KB (1,536 words) - 04:24, 30 August 2023
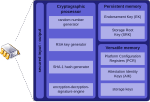
- security against firmware attacks. Trusted Platform Module (TPM) was conceived by a computer industry consortium called Trusted Computing Group (TCG). It evolved...79 KB (6,479 words) - 23:40, 8 June 2024
- Solidcore Systems)products. Among other companies bought and sold by McAfee is Trusted Information Systems, which developed the Firewall Toolkit, the free software foundation...51 KB (4,756 words) - 17:44, 20 June 2024
- Trusted Information Security Assessment Exchange (TISAX) is an assessment and exchange mechanism for the information security of enterprises, developed...2 KB (244 words) - 14:27, 26 January 2024
- Multilevel security (section Trusted operating systems)to separate information domains, that is, a system we must trust. This distinction is important because systems that need to be trusted are not necessarily...31 KB (4,178 words) - 20:28, 27 March 2024
- based on ARM TrustZone technology, conforming to the TR1 standard, were later launched, such as Trusted Foundations developed by Trusted Logic. Work on...35 KB (3,219 words) - 10:30, 23 June 2024
- Conscription and the Military System Gandhi Information Center 23638Manifesto Against Conscription and the Military SystemGandhi Information Center In the name of
- of information technology management: Team-based structures and computer-based communication systems." Journal of Management Information Systems Vol
- case study of reengineering of information systems – industry — A case study of reengineering of information systems – retail — Introduction to methodology