Beaufort cipher
This article needs additional citations for verification. (October 2009) |
The Beaufort cipher, invented by some Giovanni Sestri in early 18th century but widely attributed to Sir
Using the cipher
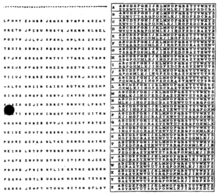
To encrypt, first choose the plaintext character from the top row of the tableau; call this column P. Secondly, travel down column P to the corresponding key letter K. Finally, move directly left from the key letter to the left edge of the tableau, the ciphertext encryption of plaintext P with key K will be there.
For example if encrypting plain text character "d" with key "m" the steps would be:
- find the column with "d" on the top,
- travel down that column to find key "m",
- travel to the left edge of the tableau to find the ciphertext letter ("K" in this case).
To decrypt, the process is reversed. Unlike the otherwise very similar
In the above example in the column with "m" on top one would find in the reciprocal "d" row the ciphertext "K". The same is true for decryption where ciphertext "K" combined with key "m" results in plaintext "d" as well as combining "K" with "d" results in "m". This results in "trigram" combinations where two parts suffice to identify the third. After eliminating the identical trigrams only 126 of the initial 676 combinations remain (see below) and could be memorized in any order (e.g. AMN can be memorized as "man" and CIP as "pic") to speed up encoding and decoding.[6]
AAZ ABY ACX ADW AEV AFU AGT AHS AIR AJQ AKP ALO AMN
BBX BCW BDV BEU BFT BGS BHR BIQ BJP BKO BLN BMM BZZ
CCV CDU CET CFS CGR CHQ CIP CJO CKN CLM CYZ
DDT DES DFR DGQ DHP DIO DJN DKM DLL DXZ DYY
EER EFQ EGP EHO EIN EJM EKL EWZ EXY
FFP FGO FHN FIM FJL FKK FVZ FWY FXX
GGN GHM GIL GJK GUZ GVY GWX
HHL HIK HJJ HTZ HUY HVX HWW
IIJ ISZ ITY IUX IVW
JRZ JSY JTX JUW JVV
KQZ KRY KSX KTW KUV
LPZ LQY LRX LSW LTV LUU
MOZ MPY MQX MRW MSV MTU
NNZ NOY NPX NQW NRV NSU NTT
OOX OPW OQV ORU OST
PPV PQU PRT PSS
QQT QRS
RRR
Algebraic description
The Beaufort cipher can be described algebraically. For example, using an encoding of the letters A–Z as the numbers 0–25 and using addition modulo 26, let be the characters of the message, be the characters of the cipher text and be the characters of the key, repeated if necessary. Then Beaufort encryption can be written,
- .
Similarly, decryption using the key ,
- .
Decrypting as a Vigenere cipher
Due to the similarities between the Beaufort cipher and the Vigenère cipher it is possible, after applying a transformation, to solve it as a Vigenère cipher. By replacing every letter in the ciphertext and key with its opposite letter (such that 'a' becomes 'z', 'b' becomes 'y' etc.; i.e. an Atbash-transformation) it can be solved like a Vigenère cipher.
Distinguished from 'variant Beaufort'
The Beaufort cipher should not be confused with the "variant Beaufort" cipher. In variant Beaufort, encryption is performed by performing the decryption step of the standard Vigenère cipher, and likewise decryption is performed by using Vigenère encryption.
References
- ^ "Did Beaufort Really Use the Beaufort Cipher?". cryptiana.web.fc2.com. Retrieved 2024-01-10.
- ^ Franksen, Ole Immanuel, Babbage and cryptography. Or, the mystery of Admiral Beaufort's cipher. Mathematics and Computers in Simulation 35 (1993) 327-367
- ^ Mollin, Richard A., An Introduction to Cryptography, page 100. Chapman & Hall/CRC, 2001
- ISBN 9783540285205.
- ISBN 9783662026274.
- ^ Rijmenants, Dirk. "One-time Pad". Cipher Machines and Cryptology. Retrieved 28 December 2020.








