Keystroke logging
Keystroke logging, often referred to as keylogging or keyboard capturing, is the action of recording (logging) the keys struck on a keyboard,[1][2] typically covertly, so that a person using the keyboard is unaware that their actions are being monitored. Data can then be retrieved by the person operating the logging program. A keystroke recorder or keylogger can be either software or hardware.
While the programs themselves are legal,
Keylogging can also be used to study keystroke dynamics[7] or human-computer interaction. Numerous keylogging methods exist, ranging from hardware and software-based approaches to acoustic cryptanalysis.
History
In the mid-1970s, the
In the 1970s, spies installed keystroke loggers in the US Embassy and Consulate buildings in Moscow.[10][11] They installed the bugs in
Soviet embassies used manual typewriters, rather than electric typewriters, for classified information—apparently because they are immune to such bugs.[12] As of 2013, Russian special services still use typewriters.[11][13][14]
Application of keylogger
Software-based keyloggers
A software-based keylogger is a computer program designed to record any input from the keyboard.
From a technical perspective, there are several categories:
- Hypervisor-based: The keylogger can theoretically reside in a malware hypervisor running underneath the operating system, which thus remains untouched. It effectively becomes a virtual machine. Blue Pill is a conceptual example.
- kernel level, which makes them difficult to detect, especially for user-mode applications that do not have root access. They are frequently implemented as rootkits that subvert the operating system kernel to gain unauthorized access to the hardware. This makes them very powerful. A keylogger using this method can act as a keyboard device driver, for example, and thus gain access to any information typed on the keyboard as it goes to the operating system.
- API-based: These keyloggers APIs inside a running application. The keylogger registers keystroke events as if it was a normal piece of the application instead of malware. The keylogger receives an eventeach time the user presses or releases a key. The keylogger simply records it.
- Form grabbing based: Web formsubmissions by recording the form data on submit events. This happens when the user completes a form and submits it, usually by clicking a button or pressing enter. This type of keylogger records form data before it is passed over the Internet.
- JavaScript-based: A malicious script tag is injected into a targeted web page, and listens for key events such as
onKeyUp(). Scripts can be injected via a variety of methods, including cross-site scripting, man-in-the-browser, man-in-the-middle, or a compromise of the remote website.[19] - Memory-injection-based: Memory Injection (SpyEye trojans use this method exclusively.[20] Non-Windows systems have protection mechanisms that allow access to locally recorded data from a remote location.[clarification needed] Remote communication may be achieved when one of these methods is used:
- Data is uploaded to a website, database or an FTP server.
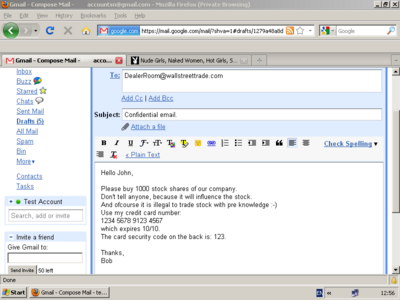
- Data is periodically emailed to a pre-defined email address.
- Data is wirelessly transmitted employing an attached hardware system.
- The software enables a remote login to the local machine from the Internet or the local network, for data logs stored on the target machine.
Keystroke logging in writing process research
Since 2006, Keystroke logging has been an established research method for the study of writing processes.[21][22] Different programs have been developed to collect online process data of writing activities,[23] including Inputlog, Scriptlog, Translog and GGXLog.
Keystroke logging is used legitimately as a suitable research instrument in several writing contexts. These include studies on cognitive writing processes, which include
- descriptions of writing strategies; the writing development of children (with and without writing difficulties),
- spelling,
- first and second language writing, and
- specialist skill areas such as translation and subtitling.
Keystroke logging can be used to research writing, specifically. It can also be integrated into educational domains for second language learning, programming skills, and typing skills.
Related features
Software keyloggers may be augmented with features that capture user information without relying on keyboard key presses as the sole input. Some of these features include:
- Clipboard logging. Anything that has been copied to the clipboardcan be captured by the program.
- Screen logging. Screenshots are taken to capture graphics-based information. Applications with screen logging abilities may take screenshots of the whole screen, of just one application, or even just around the mouse cursor. They may take these screenshots periodically or in response to user behaviors (for example, when a user clicks the mouse). Screen logging can be used to capture data inputted with an on-screen keyboard.
- Programmatically capturing the text in a API allows programs to request the text 'value' in some controls. This means that some passwords may be captured, even if they are hidden behind password masks (usually asterisks).[24]
- The recording of every program/folder/window opened including a screenshot of every website visited.
- The recording of instant messengerconversations, FTP downloads and other Internet-based activities (including the bandwidth used).
Hardware-based keyloggers

Hardware-based keyloggers do not depend upon any software being installed as they exist at a hardware level in a computer system.
- Firmware-based: BIOS-level firmware that handles keyboard events can be modified to record these events as they are processed. Physical and/or root-level access is required to the machine, and the software loaded into the BIOS needs to be created for the specific hardware that it will be running on.[25]
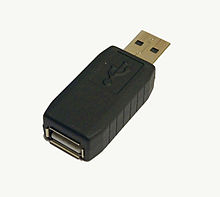
- Keyboard hardware: Hardware keyloggers are used for keystroke logging utilizing a hardware circuit that is attached somewhere in between the internal memory, which can be subsequently accessed, for example, by typing in a secret key sequence. Hardware keyloggers do not require any software to be installed on a target user's computer, therefore not interfering with the computer's operation and less likely to be detected by software running on it. However, its physical presence may be detected if, for example, it is installed outside the case as an inline device between the computer and the keyboard. Some of these implementations can be controlled and monitored remotely using a wireless communication standard.[26]
- Wireless keyboard and mouse sniffers: These passive sniffers collect packets of data being transferred from a wireless keyboard and its receiver. As encryption may be used to secure the wireless communications between the two devices, this may need to be cracked beforehand if the transmissions are to be read. In some cases, this enables an attacker to type arbitrary commands into a victim's computer.[27]
- Keyboard overlays: Criminals have been known to use keyboard overlays on ATMs to capture people's PINs. Each keypress is registered by the keyboard of the ATM as well as the criminal's keypad that is placed over it. The device is designed to look like an integrated part of the machine so that bank customers are unaware of its presence.[28]
- Acoustic keyloggers: sample is collected.[30]
- Electromagnetic emissions: It is possible to capture the receiverto tune into the specific frequency of the emissions radiated from the keyboards.
- Optical surveillance: Optical surveillance, while not a keylogger in the classical sense, is nonetheless an approach that can be used to capture passwords or PINs. A strategically placed camera, such as a hidden
- Physical evidence: For a keypad that is used only to enter a security code, the keys which are in actual use will have evidence of use from many fingerprints. A passcode of four digits, if the four digits in question are known, is reduced from 10,000 possibilities to just 24 possibilities (104 versus 4! [factorial of 4]). These could then be used on separate occasions for a manual "brute force attack".
- Smartphone sensors: Researchers have demonstrated that it is possible to capture the keystrokes of nearby computer keyboards using only the commodity accelerometer found in smartphones.[35] The attack is made possible by placing a smartphone near a keyboard on the same desk. The smartphone's accelerometer can then detect the vibrations created by typing on the keyboard and then translate this raw accelerometer signal into readable sentences with as much as 80 percent accuracy. The technique involves working through probability by detecting pairs of keystrokes, rather than individual keys. It models "keyboard events" in pairs and then works out whether the pair of keys pressed is on the left or the right side of the keyboard and whether they are close together or far apart on the QWERTY keyboard. Once it has worked this out, it compares the results to a preloaded dictionary where each word has been broken down in the same way.[36] Similar techniques have also been shown to be effective at capturing keystrokes on touchscreen keyboards[37][38][39] while in some cases, in combination with gyroscope[40][41] or with the ambient-light sensor.[42]
- Body keyloggers: Body keyloggers track and analyze body movements to determine which keys were pressed. The attacker needs to be familiar with the keys layout of the tracked keyboard to correlate between body movements and keys position. Tracking audible signals of the user' interface (e.g. a sound the device produce to informs the user that a keystroke was logged) may reduce the complexity of the body keylogging algorithms, as it marks the moment at which a key was pressed.[43]
Cracking
Writing simple software applications for keylogging can be trivial, and like any nefarious computer program, can be distributed as a trojan horse or as part of a virus. What is not trivial for an attacker, however, is installing a covert keystroke logger without getting caught and downloading data that has been logged without being traced. An attacker that manually connects to a host machine to download logged keystrokes risks being traced. A trojan that sends keylogged data to a fixed e-mail address or IP address risks exposing the attacker.
Trojans
Researchers Adam Young and Moti Yung discussed several methods of sending keystroke logging. They presented a deniable password snatching attack in which the keystroke logging trojan is installed using a virus or
Use by police
In 2000, the
Countermeasures
The effectiveness of countermeasures varies because keyloggers use a variety of techniques to capture data and the countermeasure needs to be effective against the particular data capture technique. In the case of Windows 10 keylogging by Microsoft, changing certain privacy settings may disable it.
Keylogger program authors may be able to update their program's code to adapt to countermeasures that have proven effective against it.
Anti-keyloggers
An anti-keylogger is a piece of software specifically designed to detect keyloggers on a computer, typically comparing all files in the computer against a database of keyloggers, looking for similarities which might indicate the presence of a hidden keylogger. As anti-keyloggers have been designed specifically to detect keyloggers, they have the potential to be more effective than conventional antivirus software; some antivirus software do not consider keyloggers to be malware, as under some circumstances a keylogger can be considered a legitimate piece of software.[49]
Live CD/USB
Rebooting the computer using a Live CD or write-protected Live USB is a possible countermeasure against software keyloggers if the CD is clean of malware and the operating system contained on it is secured and fully patched so that it cannot be infected as soon as it is started. Booting a different operating system does not impact the use of a hardware or BIOS based keylogger.
Anti-spyware / Anti-virus programs
Many
No software-based anti-spyware application can be 100% effective against all keyloggers.[50] Software-based anti-spyware cannot defeat non-software keyloggers (for example, hardware keyloggers attached to keyboards will always receive keystrokes before any software-based anti-spyware application).
The particular technique that the anti-spyware application uses will influence its potential effectiveness against software keyloggers. As a general rule, anti-spyware applications with
Network monitors
Network monitors (also known as reverse-firewalls) can be used to alert the user whenever an application attempts to make a network connection. This gives the user the chance to prevent the keylogger from "phoning home" with their typed information.
Automatic form filler programs
Automatic form-filling programs may prevent keylogging by removing the requirement for a user to type personal details and passwords using the keyboard.
One-time passwords (OTP)
Using one-time passwords may prevent unauthorized access to an account which has had its login details exposed to an attacker via a keylogger, as each password is invalidated as soon as it is used. This solution may be useful for someone using a public computer. However, an attacker who has remote control over such a computer can simply wait for the victim to enter their credentials before performing unauthorized transactions on their behalf while their session is active.
Another common way to protect access codes from being stolen by keystroke loggers is by asking users to provide a few randomly selected characters from their authentication code. For example, they might be asked to enter the 2nd, 5th, and 8th characters. Even if someone is watching the user or using a keystroke logger, they would only get a few characters from the code without knowing their positions.[51]
Security tokens
Use of smart cards or other security tokens may improve security against replay attacks in the face of a successful keylogging attack, as accessing protected information would require both the (hardware) security token as well as the appropriate password/passphrase. Knowing the keystrokes, mouse actions, display, clipboard, etc. used on one computer will not subsequently help an attacker gain access to the protected resource. Some security tokens work as a type of hardware-assisted one-time password system, and others implement a cryptographic challenge–response authentication, which can improve security in a manner conceptually similar to one time passwords. Smartcard readers and their associated keypads for PIN entry may be vulnerable to keystroke logging through a so-called supply chain attack[52] where an attacker substitutes the card reader/PIN entry hardware for one which records the user's PIN.
On-screen keyboards
Most on-screen keyboards (such as the on-screen keyboard that comes with Windows XP) send normal keyboard event messages to the external target program to type text. Software key loggers can log these typed characters sent from one program to another.[53]
Keystroke interference software
Keystroke interference software is also available.[54] These programs attempt to trick keyloggers by introducing random keystrokes, although this simply results in the keylogger recording more information than it needs to. An attacker has the task of extracting the keystrokes of interest—the security of this mechanism, specifically how well it stands up to cryptanalysis, is unclear.
Speech recognition
Similar to on-screen keyboards, speech-to-text conversion software can also be used against keyloggers, since there are no typing or mouse movements involved. The weakest point of using voice-recognition software may be how the software sends the recognized text to target software after the user's speech has been processed.
Handwriting recognition and mouse gestures
Many
The same potential weakness of speech recognition applies to this technique as well.
Macro expanders/recorders
With the help of many programs, a seemingly meaningless text can be expanded to a meaningful text and most of the time context-sensitively, e.g. "en.wikipedia.org" can be expanded when a web browser window has the focus. The biggest weakness of this technique is that these programs send their keystrokes directly to the target program. However, this can be overcome by using the 'alternating' technique described below, i.e. sending mouse clicks to non-responsive areas of the target program, sending meaningless keys, sending another mouse click to the target area (e.g. password field) and switching back-and-forth.
Deceptive typing
Alternating between typing the login credentials and typing characters somewhere else in the focus window
Another very similar technique uses the fact that any selected text portion is replaced by the next key typed. e.g., if the password is "secret", one could type "s", then some dummy keys "asdf". These dummy characters could then be selected with the mouse, and the next character from the password "e" typed, which replaces the dummy characters "asdf".
These techniques assume incorrectly that keystroke logging software cannot directly monitor the clipboard, the selected text in a form, or take a screenshot every time a keystroke or mouse click occurs. They may, however, be effective against some hardware keyloggers.
See also
- Anti-keylogger
- Black-bag cryptanalysis
- Computer surveillance
- Cybercrime
- Digital footprint
- Hardware keylogger
- Reverse connection
- Session replay
- Spyware
- Trojan horse
- Virtual keyboard
- Web tracking
References
- S2CID 8161528.
- S2CID 238703970.
- ^ Use of legal software products for computer monitoring, keylogger.org
- ^ "Keylogger". Oxford dictionaries. Archived from the original on 2013-09-11. Retrieved 2013-08-03.
- ^ Keyloggers: How they work and how to detect them (Part 1), Secure List, "Today, keyloggers are mainly used to steal user data relating to various online payment systems, and virus writers are constantly writing new keylogger Trojans for this very purpose."
- S2CID 252849669.
- ^ Stefan, Deian, Xiaokui Shu, and Danfeng Daphne Yao. "Robustness of keystroke-dynamics based biometrics against synthetic forgeries." computers & security 31.1 (2012): 109-121.
- ^ "Selectric bug".
- ^ "The Security Digest Archives". Retrieved 2009-11-22.
- ^ "Soviet Spies Bugged World's First Electronic Typewriters". qccglobal.com. Archived from the original on 2013-12-20. Retrieved 2013-12-20.
- ^ a b Geoffrey Ingersoll. "Russia Turns To Typewriters To Protect Against Cyber Espionage". 2013.
- ^ a b Sharon A. Maneki. "Learning from the Enemy: The GUNMAN Project" Archived 2017-12-03 at the Wayback Machine. 2012.
- ^ Agence France-Presse, Associated Press (13 July 2013). "Wanted: 20 electric typewriters for Russia to avoid leaks". inquirer.net.
- ^ Anna Arutunyan. "Russian security agency to buy typewriters to avoid surveillance" Archived 2013-12-21 at the Wayback Machine.
- ^ "What is a Keylogger?". PC Tools.
- ^ Caleb Chen (2017-03-20). "Microsoft Windows 10 has a keylogger enabled by default – here's how to disable it".
- Symantec. 2005-11-26: 23–24. Retrieved 2011-03-25.)
{{cite journal}}: Cite journal requires|journal=(help - ^ Jonathan Brossard (2008-09-03). "Bypassing pre-boot authentication passwords by instrumenting the BIOS keyboard buffer (practical low level attacks against x86 pre-boot authentication software)" (PDF). www.ivizsecurity.com. Archived from the original (PDF) on 2008-09-13. Retrieved 2008-09-23.
{{cite journal}}: Cite journal requires|journal=(help) - ^ "Web-Based Keylogger Used to Steal Credit Card Data from Popular Sites". Threatpost | The first stop for security news. 2016-10-06. Retrieved 2017-01-24.
- ^ "SpyEye Targets Opera, Google Chrome Users". Krebs on Security. Retrieved 26 April 2011.
- ^ K.P.H. Sullivan & E. Lindgren (Eds., 2006), Studies in Writing: Vol. 18. Computer Key-Stroke Logging and Writing: Methods and Applications. Oxford: Elsevier.
- ISBN 9781848729636
- ^ Vincentas (11 July 2013). "Keystroke Logging in SpyWareLoop.com". Spyware Loop. Archived from the original on 7 December 2013. Retrieved 27 July 2013.
- ^ Microsoft. "EM_GETLINE Message()". Microsoft. Retrieved 2009-07-15.
- ^ "Apple keyboard hack". Digital Society. Archived from the original on 26 August 2009. Retrieved 9 June 2011.
- ^ "Keylogger Removal". SpyReveal Anti Keylogger. Archived from the original on 29 April 2011. Retrieved 25 April 2011.
- ^ "Keylogger Removal". SpyReveal Anti Keylogger. Retrieved 26 February 2016.
- ^ Jeremy Kirk (2008-12-16). "Tampered Credit Card Terminals". IDG News Service. Retrieved 2009-04-19.
- ^ Andrew Kelly (2010-09-10). "Cracking Passwords using Keyboard Acoustics and Language Modeling" (PDF).
- ^ Sarah Young (14 September 2005). "Researchers recover typed text using audio recording of keystrokes". UC Berkeley NewsCenter.
- ^ Knight, Will. "A Year Ago: Cypherpunks publish proof of Tempest | ZDNet". ZDNet.
- ^ Martin Vuagnoux and Sylvain Pasini (2009-06-01). Vuagnoux, Martin; Pasini, Sylvain (eds.). "Compromising Electromagnetic Emanations of Wired and Wireless Keyboards". Proceedings of the 18th Usenix Security Symposium.
- ^ "ATM camera". www.snopes.com. 19 January 2004. Retrieved 2009-04-19.
- ISBN 978-1-4577-2155-7.
- .
- ^ "iPhone Accelerometer Could Spy on Computer Keystrokes". Wired. 19 October 2011. Retrieved August 25, 2014.
- .
- ISBN 9781450313124.
- ^ Cai, Liang; Chen, Hao (2011). TouchLogger: inferring keystrokes on touch screen from smartphone motion (PDF). Proceedings of the 6th USENIX conference on Hot topics in security. USENIX. Retrieved 25 August 2014.
- .
- .
- .
- ^ Hameiri, Paz (2019). "Body Keylogging". Hakin9 IT Security Magazine. 14 (7): 79–94.
- S2CID 14768587.
- S2CID 12179472.
- ^ John Leyden (2000-12-06). "Mafia trial to test FBI spying tactics: Keystroke logging used to spy on mob suspect using PGP". The Register. Retrieved 2009-04-19.
- ^ John Leyden (2002-08-16). "Russians accuse FBI Agent of Hacking". The Register.
- ^ Alex Stim (2015-10-28). "3 methods to disable Windows 10 built-in Spy Keylogger".
- ^ "What is Anti Keylogger?". 23 August 2018.
- .
- ISSN 0167-4048.
- ^ Austin Modine (2008-10-10). "Organized crime tampers with European card swipe devices". The Register. Retrieved 2009-04-18.
- ^ Scott Dunn (2009-09-10). "Prevent keyloggers from grabbing your passwords". Windows Secrets. Retrieved 2014-05-10.
- ^ Christopher Ciabarra (2009-06-10). "Anti Keylogger". Networkintercept.com. Archived from the original on 2010-06-26.
- ^ Cormac Herley and Dinei Florencio (2006-02-06). "How To Login From an Internet Cafe Without Worrying About Keyloggers" (PDF). Microsoft Research. Retrieved 2008-09-23.
External links
![]() Media related to Keystroke logging at Wikimedia Commons
Media related to Keystroke logging at Wikimedia Commons
- Keyloggers at Curlie

